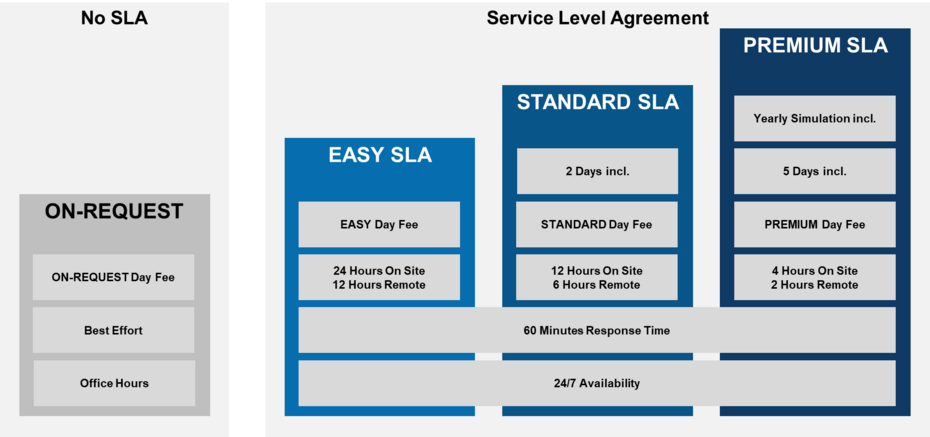
Our incident response service hotline provides 24-hour, all-day-of-the-year access to top incident responders and digital forensic specialists who can immediately support your task force in the event of a cyber emergency. Thanks to our prior on-boarding, guaranteed response time, as well as our constant availability, you save time where it matters. In addition, we conduct regular simulations with you and your organization in order to further optimize and improve our joint relationship, to keep a cool head in case of emergency and to protect you from the worst-case scenario.
Analysis
Our DFIR specialists have been explicitly trained to respond to incidents and suspicious activities. In case of an emergency, we help
- contain the infrastructure,
- prevent further spreading,
- kill the entry path and propose immediate measures,
- analyze the system for malware,
- identify and isolate devices,
- hunt the entire fleet and collect evidence.
Our team is available around the clock to support you in case of suspected breaches and to plan the next steps.
On-boarding
On-boarding ensures that our DFIR specialists focus on the incident rather than wasting time understanding your infrastructure, gaining access and deal with legal and compliance matters. A dedicated contact person (single point of contact) ensures that all our information is kept up-to-date and that we keep track of the major changes in your environment.
We ensure that all important questions and requirements are clarified in advance:
- All contact persons are defined.
- Reporting of incidents is regulated.
- Secure data exchange and continuous flow of information are ensured.
- Accesses are prepared.
- Important documentation / concepts and topologies are available.
- Critical assets and scenarios are known.
- Our tooling is tailored to work in your environment.
Expert Panel
With access to the Compass Security Expert Panel, security-relevant questions, decisions and actions can be backed up and challenged with the help of our security specialist team. You will receive competent recommendations and suggestions that will help you to implement immediate measures.
Simulation
Regular tabletop exercises of real-life scenarios help to train your blue team. The simulation aims to make involved people understand their responsibilities. It challenges their ability to really get tasks done and tests whether cooperation among the members is efficient. Moreover, it helps us to understand whether requested data and artifacts really contain the information we need to follow up leads during an investigation. After the exercise, the results are discussed with the client and an action item list is drawn up to improve the readiness of the entire organization.